This is a live article, we will update more as we learn more about the exploit. Since the log4j attack is at the application layer, we are not claiming Firewalla will fully protect and solve this exploit; Firewalla is just one piece of the puzzle protecting you on the network side.
Is Firewalla Box or App vulnerable to this exploit?
No.
Firewalla code does not use Java, Firewalla Android app (Java) does not use Log4j, so there is nothing in Firewalla's codebase that is vulnerable to the Log4j zero-day exploit. For additional detail on this threat, see this article.
How does this exploit work?
The exploit utilizes a bug in the widely used Apache Log4j component to inject software into the target system. https://www.zdnet.com/article/log4j-zero-day-flaw-what-you-need-to-know-and-how-to-protect-yourself/
Why is this exploit critical?
- log4j component is widely used in many-many Java applications. Most popular in enterprise and cloud services.
- This vulnerability is relatively simple to exploit.
Are my devices impacted?
Java is being used by many devices in both corporate and homes. Here are some articles:
- https://www.cyber.nj.gov/alerts-advisories/log4j-vulnerability-being-actively-exploited
- https://help.minecraft.net/hc/en-us/articles/4416199399693-Security-Vulnerability-in-Minecraft-Java-Edition
Even if your device does not run java/log4j, it is highly possible that the web/cloud services that are being used may use java/log4j.
How to prevent these attacks?
- Keep all of your devices up to date with security patches from the device vendor. In particular, some wifi and switch controllers may require updating especially those that are managed through the cloud.
- If you are running web services inside of your home or business, make sure you understand how to patch log4j.
How can Firewalla help?
Firewalla by default should have these three mechanisms already to protect:
- Firewalla ingress firewall (traffic from the internet to your network) will block any attack originating from the internet side. (unless you explicitly open the ports)
- Our cloud will dynamically update the latest signatures of the attacks, once your device starts to load the attacking payload, it will be blocked via the egress firewall. (traffic from inside out)
- Even the firewalla can't see all the applications, there are still various alarms in the system that will trigger if anything out of the ordinary happens.
Here are more ways you can actively be protect
Due to the large attack surface of the Log4j exploit, it is highly likely that this exploit may happen to your devices directly and/or the cloud services that these devices are connecting to. When this happens, it will require different ways to detect the problem caused by this exploit.
Here are some additional tips on how your Firewalla can help secure your network, in case you have vulnerable devices.
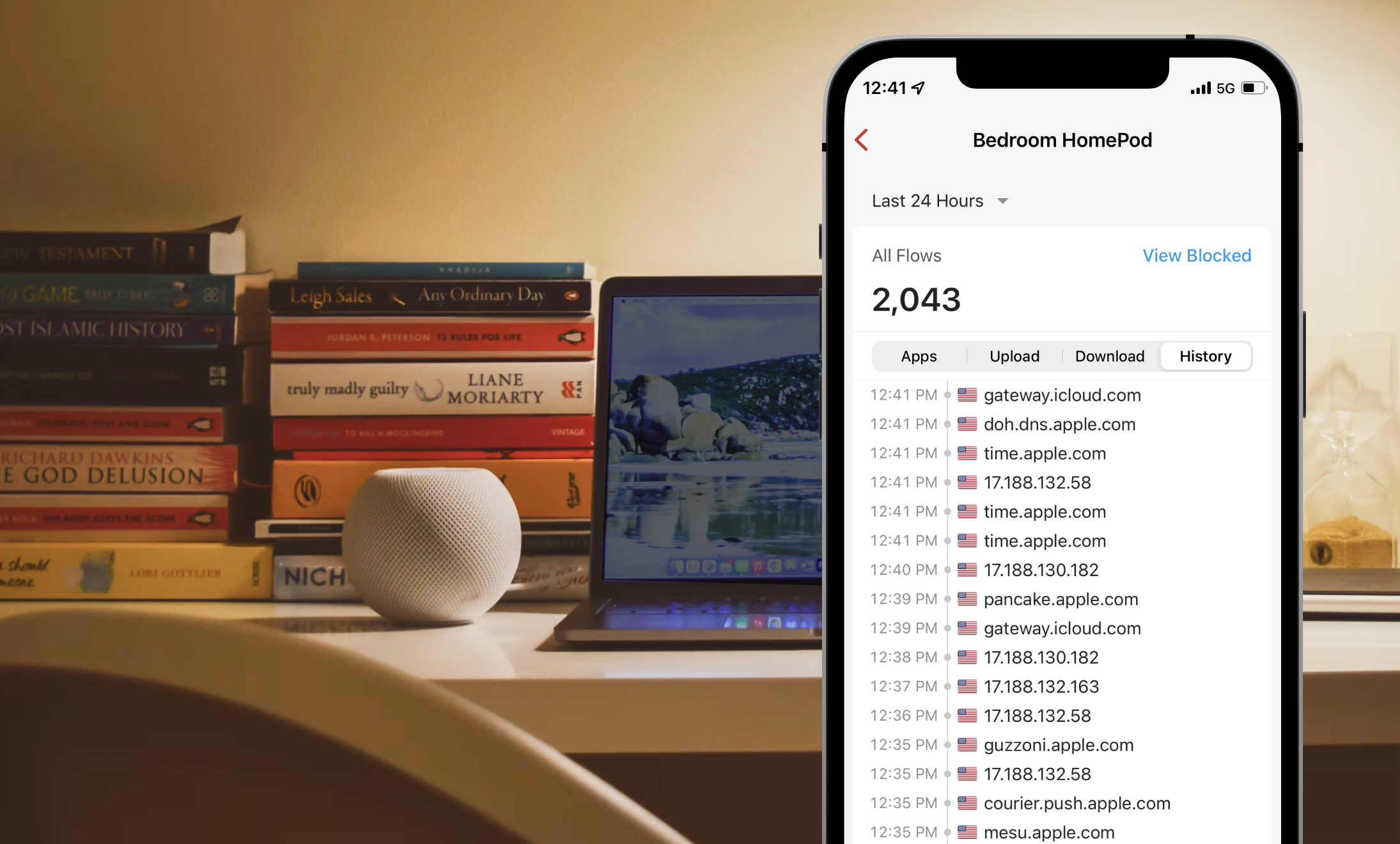
- Deep Insight and Visibility: see what your devices are doing
- Controls: The ability to prepare your network to be 'secure'
- Protect: Automatically protect your network
Visibility:
- Watch out for unusual network activities from your devices. It may be a sign of something not good.
- Use the open port button to see if you have anything open in your network.
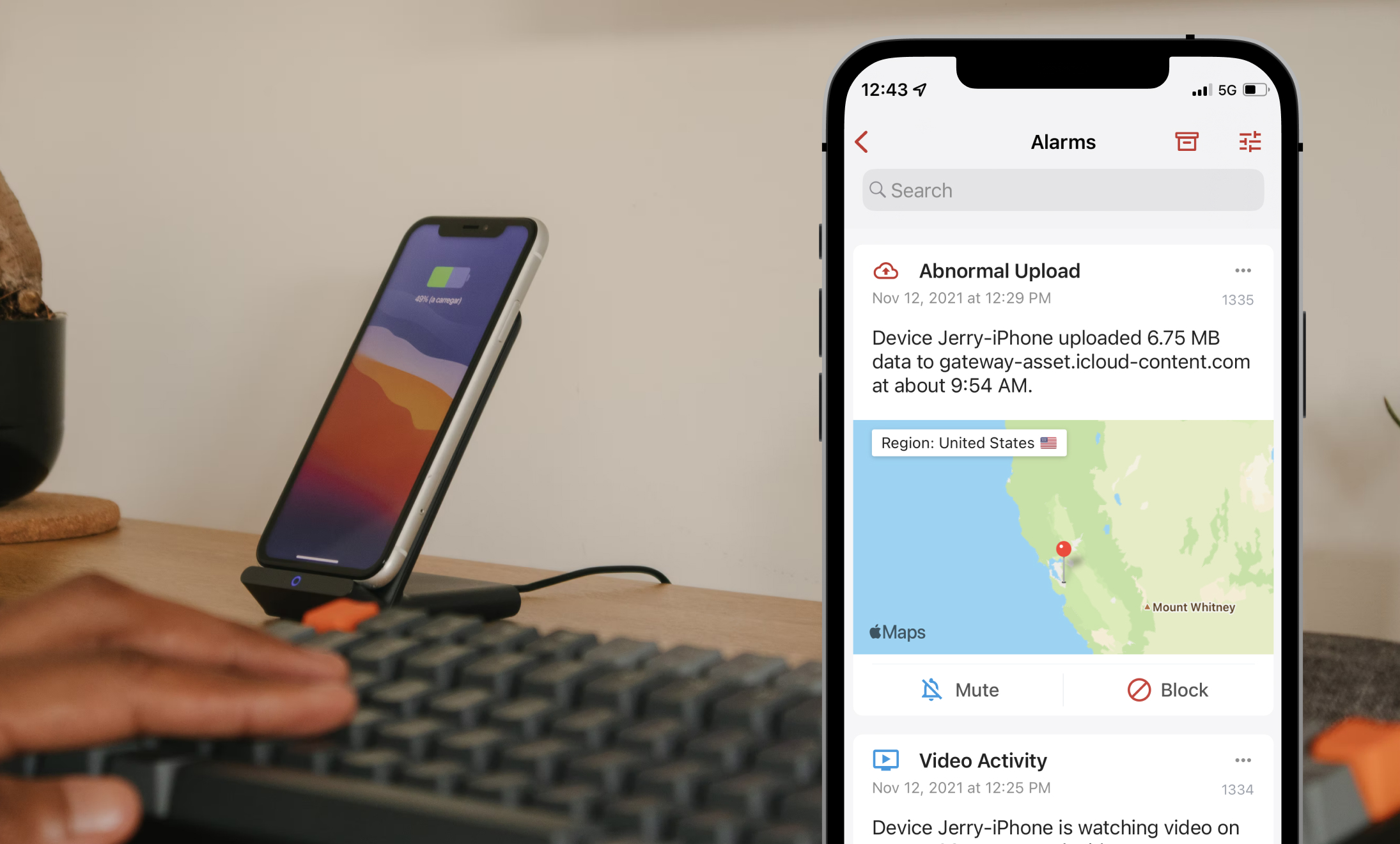
Alarms:
- Watch out for unexpected port open alarms. If you see any, it probably makes sense to turn on some of the rules to block regions.
- Be a bit more aware of the Firewalla upload alarms. These are behavioral, and if you see anything strange, block it.
- Watch out for unusual alarms. Some of the exploits may manifest here.
Controls:
Your network needs to be secure by default, this is how the different ways Firewalla can control your network via different control policies.
- If Monitoring is set to Router mode, make sure you do not remove the block "Traffic from Internet" rule. This is your default firewall to prevent traffic from coming into your network.
- Turn off UPnP (Network → NAT Settings → Port Forwarding → UPnP). This prevents 'hacked' devices from using your home network to run other services.
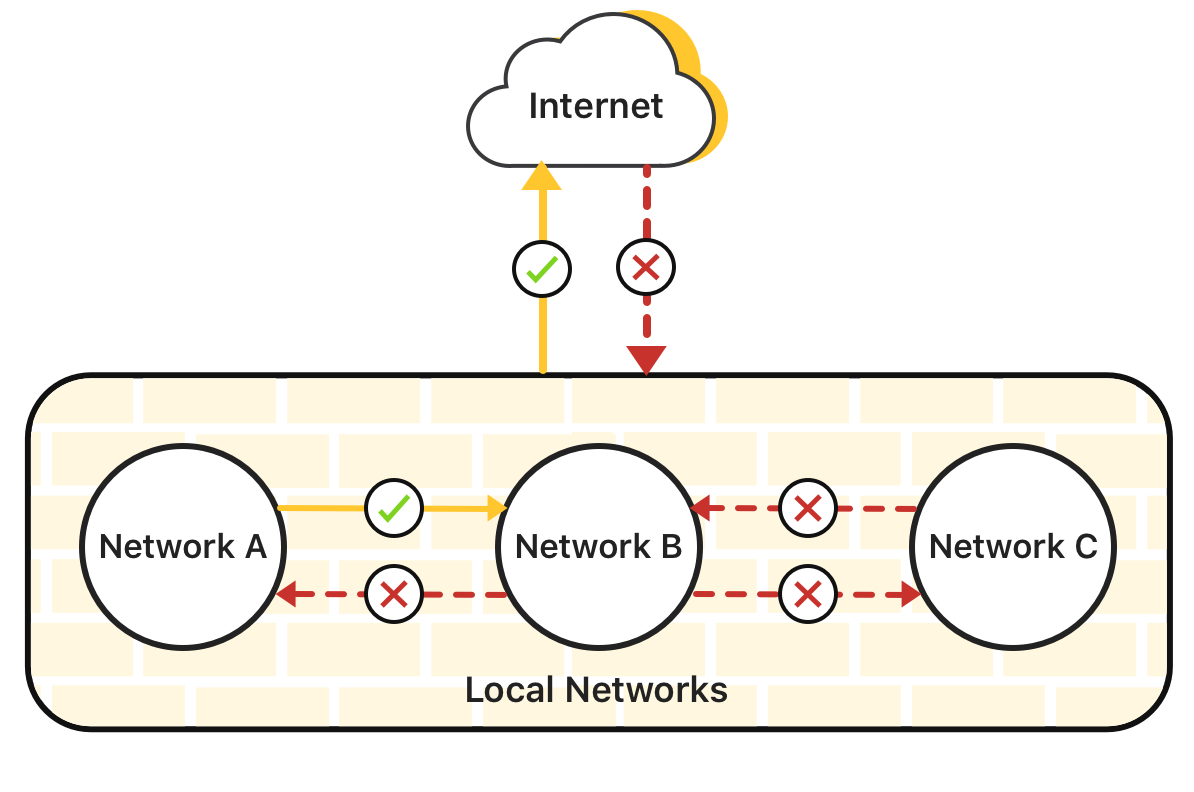
- If possible use network segmentation to split your network into segments. This prevents a hack to spread in your network.
- Add regional blocks to your network, to block countries off.
- Firewalla can also control traffic going from your home out, see rules.
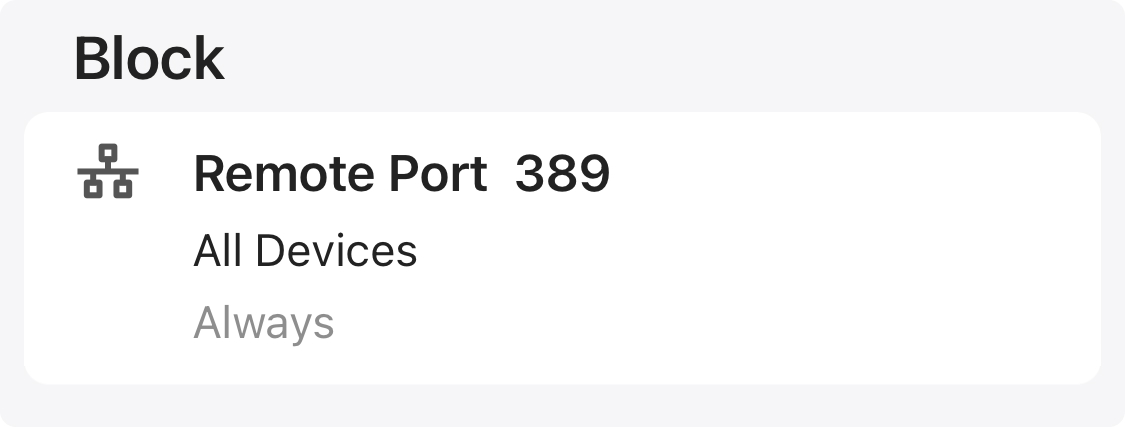
- Block LDAP Port 389. Some exploit may use this default port; LDAP is usually not used in residential or small businesses on the WAN side. You may also want to block LDAPS Port 636.
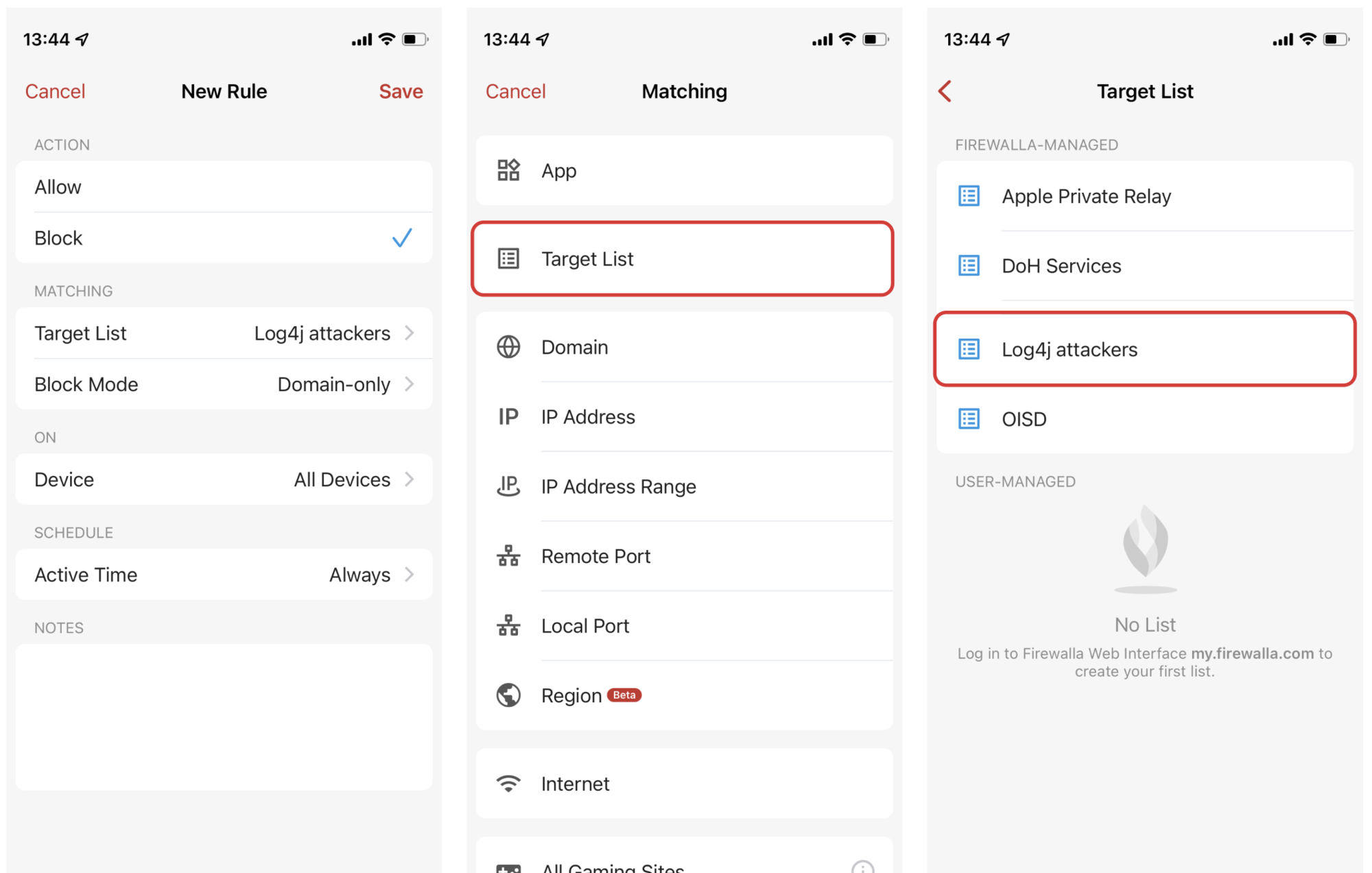
- Firewalla security intel already included some of the log4j attackers. Since this exploit is evolving very faster, we also created a dynamic "Log4j attackers" target list from publicly available sources. This list may have more false positives. (To use target lists, please see https://help.firewalla.com/hc/en-us/articles/1500005941962-Firewalla-Feature-Target-List)
Protect:
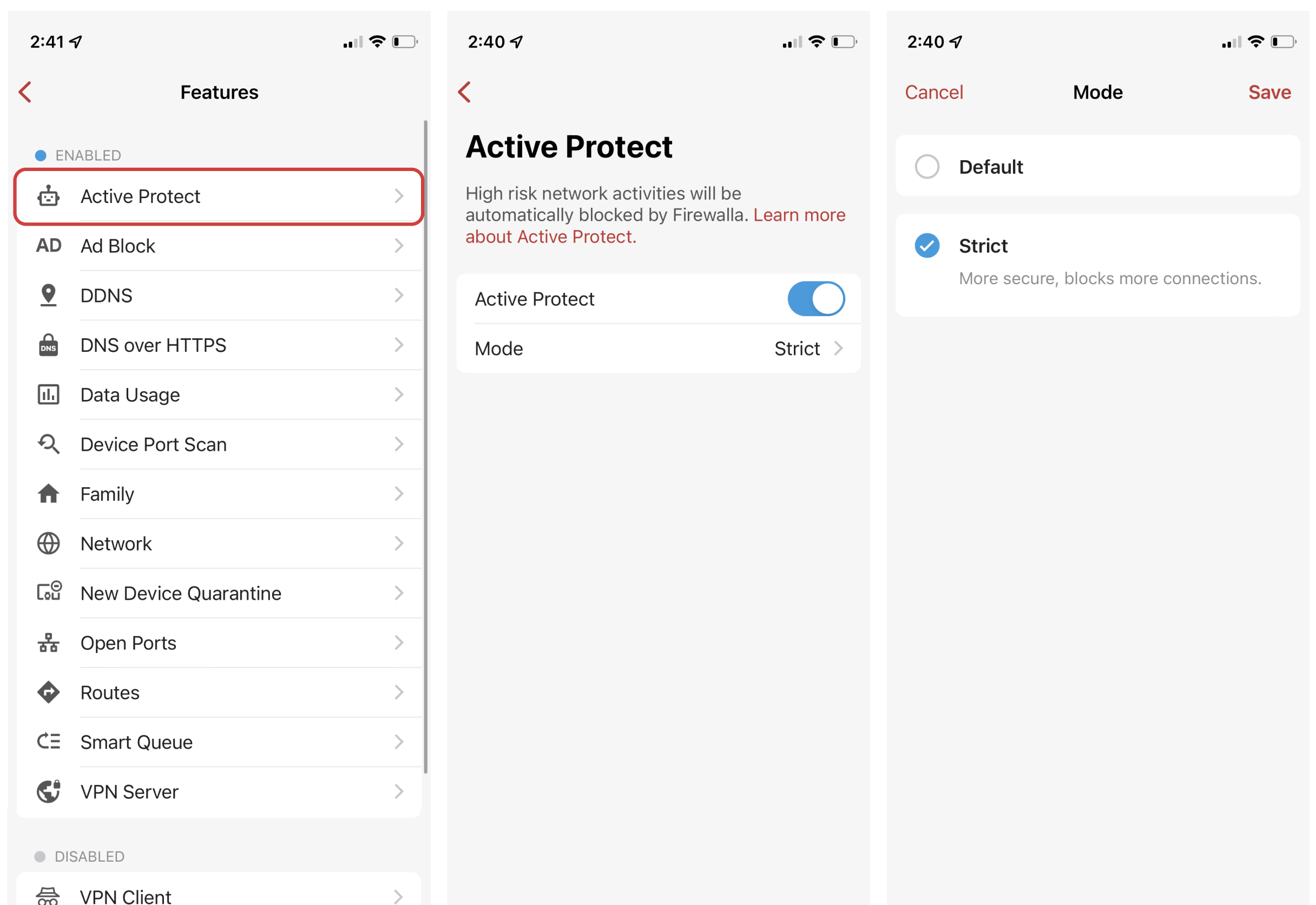
- Do not turn off "active protect", this feature is there to block 'bad' stuff automatically.
- Always try your best to use Firewalla VPN server to access your home or business when outside.
- If you have Firewalla Gold/Purple, set Active Protect to Strict mode. This mode will block more traffic from sites already hacked.
Firewalla Containers:
If you have installed any additional software on your Firewalla, be sure that it is not vulnerable or update it immediately to be sure that your network is safe. For example, if you run the UniFi Network application (controller) in docker on your Firewalla, or on your network, be sure to update it to Version 6.5.55 or newer as it was recently updated to address Log4j specifically. See Guide: How to run UniFi Controller on the Firewalla Gold or Purple for update instructions.
We will add additional tips, as we learn more about this exploit ourselves.

Comments
1 comment
Will log4j attack show up as a tls heart bleed attack I have recently seen being blocked on my Firewalla ?
Please sign in to leave a comment.