Firewalla Policy-Based Routing (PBR) is a powerful feature that allows you to manage where your networking traffic goes. When PBR is integrated with VPN and Multi-WAN features, it's a very effective tool for fully controlling your network traffic.
Learn more about Firewalla Policy-Based Routing.
In this article, we will show you how to selectively route your traffic to:
- Setting up a Third-Party VPN with Firewalla VPN Client
- Testing a VPN Connection
- Example 1: Route all video streaming traffic to a Third-Party VPN
- Example 2: Route all traffic to a Third-Party VPN for privacy
- Example 3: Route all traffic to a VPN, but route banking to a Third-Party VPN
- Example 4: Route work traffic to a VPN and personal traffic to your WAN
- Example 5: VPN to your Third-Party VPN when you're away from home
- About Multi-WAN setups
- Example 6: Route video conferencing over a better-performing WAN
- Example 7: Route Hulu over a specific WAN to avoid fraud alerts
- Example 8: Route IoT devices that don’t handle Multi-WAN well
Third-Party VPNs
Firewalla's VPN Client feature connects any device— or even your entire local network— to a VPN server. It can be used in various ways to protect your privacy and improve security. The examples below demonstrate how to create a VPN Client connection and route different traffic through a VPN.
Setting up a Third-Party VPN in Firewalla VPN Client
The first step for all the following examples is to set up a third-party VPN in the Firewalla VPN Client. See our article on Firewalla VPN Client for details.
If you just want to send all traffic from a network or device through a third-party VPN, you do not need to use the Routes feature. Using VPN Client + Routes allows you to selectively route different types of traffic.
Testing a VPN Connection
To test a VPN connection, you can use a service that reports your external IP address. There are many available but https://ipinfo.io/ is very detailed. You can also just Google "what is my IP address?"
Do this before you attempt to follow any of the examples below. Then, test again after completing one of the example scenarios and compare your results to see if your VPN connection works
Example 1: Route all video streaming traffic to a Third-Party VPN
In this example, we are going to route all video streaming traffic from all devices through a VPN with the assistance of Policy-Based Routing.
- Edit your VPN client. In this case, leave Apply To blank (0 devices).
- Launch Routes and add a new Route.
- Matching: choose from Target List, Domain, IP Address, IP Range, Remote Port, Region, Internet, Gaming, Social, or Video. To block all video sites, select Video.
- On: choose what Device(s) or Group(s) you want to be included on this Route.
- Interface: choose the VPN you want to use.
- Route Preference: select either Static, which drops the traffic if the selected interface is not available; or Preferred, which allows the traffic through an alternate route if the selected interface is not available. In this case, we'll select Preferred so that we can watch videos even if the VPN is unavailable.
- Save.
Note that in this case, we can't verify our VPN by checking our IP address because we asked for only video traffic to use VPN, so ipinfo.io and Google won't see the VPN IP.
Result: All video traffic for all devices on the network will go through the selected VPN.
Example 2: Route all traffic to a Third-Party VPN for privacy
In this example, we route all internet traffic through a VPN to keep our location private since an IP address can disclose an approximate location. This is similar to Example 1, but it affects all traffic on all devices on our Primary LAN.
- Edit the VPN Client connection and Apply To all devices.
- Verify your IP address from one of the devices you included above by Googling "What's my IP" or using a service like https://ipinfo.com.
Result: All WAN traffic for all devices on our Primary LAN will go through the selected VPN. You can select more than one network segment if you like.
Example 3: Route all traffic to a VPN, but route banking to a Third-Party VPN
Now say you wanted to run all WAN traffic through a VPN except your bank's website. This is the inverse of the previous case. You could accomplish this as follows.
- Set up your VPN Client and Apply To the device(s) that you want to route to the VPN.
- Create a Route.
- Matching: specify a Domain, in this case, your bank.
- On: select the devices that should use the route to.
- Interface: choose your WAN.
- Route Preference: choose between Static or Preferred.
- Save the Route.
In the middle image in the row of screenshots below, we are sending all traffic on only device "MacBook-Pro-2" to the VPN except "bigbank.com". In the rightmost image, we are sending all traffic on all devices to the VPN except traffic to bigbank.com.
Policy-based routing can be very flexible and allow you to configure VPN connections that automatically do what is needed without the person using the device having to know anything about VPNs or remembering to turn them on and off.
To verify your VPN is working as expected, check the IP address from one of the devices you included above by googling "What's my IP" or using a service like, https://ipinfo.com.
Result: All WAN traffic for all devices on the network will go through the selected VPN except for a specified domain.
Example 4: Route work traffic to a VPN and personal traffic to your WAN
In this example, we are going to route all traffic from specific devices to your company over a VPN. This is ideal if you want to send communications from your work laptop, tablet, or phone over VPN. No other devices will be able to connect to the VPN and all traffic that isn't work-related will go over the normal WAN connection. This is much more seamless and convenient than having to start a VPN session on each of your devices just to check in some code or review a sensitive work document. It also doesn't send personal internet traffic through your company.
- Edit the VPN Client connection and Apply To the device(s) or device group(s) you want to connect to your work VPN.
- Create a Route.
- Matching: set your company domain.
- On: choose the Device(s) or Group(s) you want to be included.
- Interface: choose your work VPN.
- Route Preference: choose between Static or Preferred.
- Save.
In this case, you can verify your VPN by accessing the domains you specified. If you can access them, your VPN is working.
Note that this is a great place to use Target Lists. For example, let's say your work has three second-level domains that you need to be able to access via VPN because your company IT department has restricted access. Instead of creating a Route for each domain, you could create a Target List with all your domains and use that to create just one Route.
Result: All traffic to your work domains on your work devices will go through the selected VPN. No other devices will be able to access the VPN. Traffic that is not work-related will not go over the VPN or through your company's network.
Example 5: VPN to your Third-Party VPN when you're away from home
In this example, we're going to use both Firewalla's VPN Server and VPN Client to connect our devices to a Third-Party VPN even when we're away from our local network. There are two VPN connections here:
- A VPN from your device to your home.
- A VPN from your home to a third-party VPN.
First, set up a VPN Client connection to your Third-Party VPN and set up the Firewalla VPN Server. Then, create a new Route and select:
- Matching: Internet Traffic
- On: Select your VPN Server (the VPN network you're VPN-ing into)
- Interface: Select your VPN Client (your Third-Party VPN)
Result: When you VPN to your home network while traveling, you are automatically connected to a Third-Party VPN server, protecting your privacy and connecting you to private networks.
Multi-WAN Examples
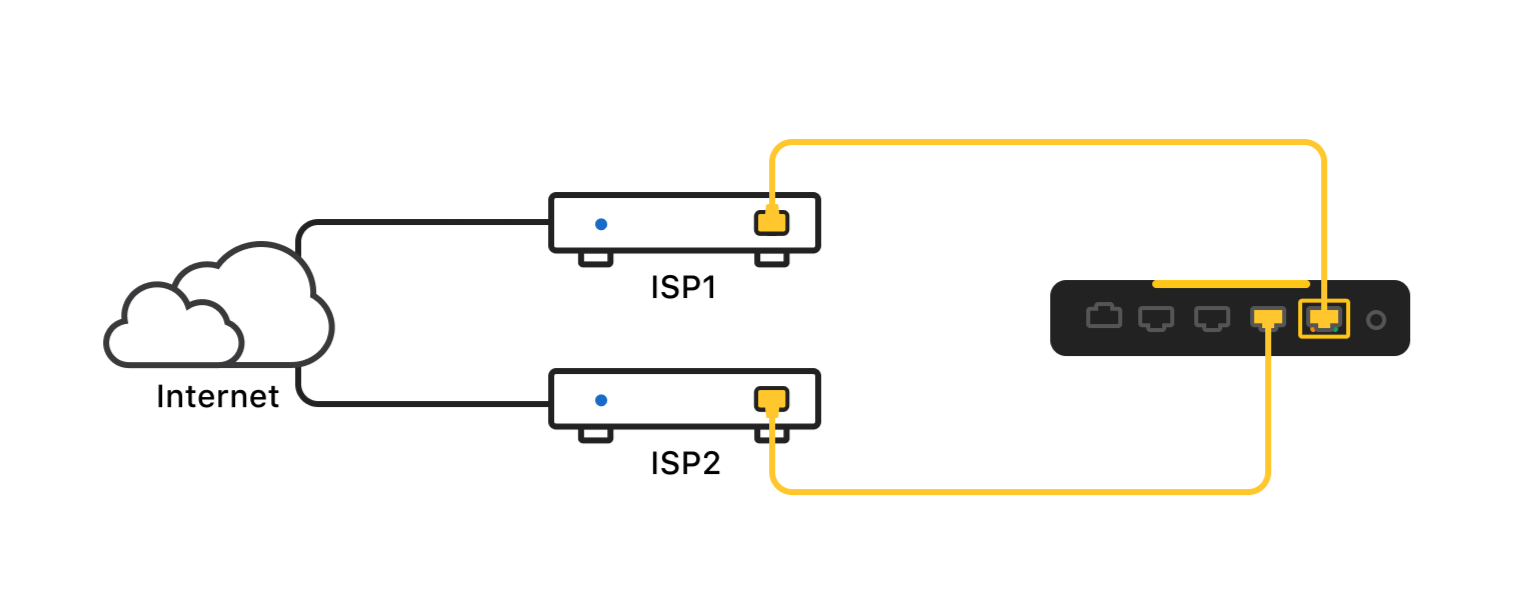
Multi-WAN setups are when users have multiple WAN connections for redundancy and increased throughput.
To support Multi-WAN setups, Firewalla offers two different WAN usage modes:
-
Failover mode (use ISP1 unless the connection is faulty; then use ISP2)
- Load balancing mode (e.g. direct 80% of WAN traffic to ISP1 and direct the rest to ISP2)
This is a powerful feature, but sometimes it needs the assistance of other features to get around some challenges. In the examples below, we will demonstrate ways to Routes to selectively direct traffic through different WANs.
Example 6: Route video conferencing over a better-performing WAN
Not all networks are equally capable. Some networks have greater upload speeds than others. Some networks are faster than others. And of course, some have data caps. Rather than the simple load balancing mentioned above, which splits a percentage of total network traffic between the WANs, you can select particular applications to go over one WAN or another. For example, you might direct video conferencing traffic like Zoom over ISP 1 and put email, IoT, and an alarm system on ISP 2 to ensure that video conferencing is the best possible quality.
This can also be used in conjunction with Smart Queue. Here's an example of a Route directing all traffic from Zoom over a specific WAN:
- Matching: Domain "zoom.us"
- On: All devices
- Interface: WAN "WAN"
- Route Preference: Preferred (in case "WAN" isn't available, your video conferencing traffic will still go through)
Result: You can control which network specific types of traffic travel on. You can also choose to use a VPN when necessary, keeping applications on your network performing at their best.
Example 7: Route Hulu over a specific WAN to avoid fraud alerts
Some video streaming services use your IP address to detect if you have broken their ToS (Terms of Service) by using their service from different locations. If you have a multi-WAN setup, sometimes your IP address will show as belonging to ISP1 and other times ISP2 even if you haven't moved your device and you aren't doing anything wrong. This is easily solved using Routing.
Create a Route with the following specifications:
- Matching: Domain; in this case, we will use hulu.com
- On: Choose the Device(s) or Group(s) that are affected by this rule
- Interface: Choose the WAN you want to use
- Route Preference: choose between Static or Preferred.
Save the Route. Now, all traffic to Hulu will go over the selected ISP.
Result: By using Policy-Based Routing, traffic to a Video Streaming service can be forced to use a specific WAN port. This keeps the IP address the same, avoiding fraud alerts.
Example 8: Route IoT devices that don’t handle Multi-WAN well
Some IoT devices will have problems if you have a multi-WAN configuration. The solution is to route them to a specific WAN. You can create a Route like this for your IoT devices:
- Matching: Traffic to Internet
- On: IoT device or device group
- Interface: WAN
- Route Preference: choose between Static or Preferred
This will send all traffic from those devices to the selected WAN interface. Of course, as discussed previously, you could send traffic for these devices to a VPN instead.
Important Notes
- More than one VPN can be operational at the same time, but any single device cannot be routed through more than one VPN at the same time.
- You can have VPN Server and VPN Client running at the same time.
- You can specify any type of traffic and route it to a Third-Party VPN server (as long as the VPN is connected).
- If you have a multi-WAN setup, you can route any traffic to any WAN connection no matter if the WANs are set to failover or load balancing.
Related links
Please send feedback to help@firewalla.com if you would like to see more detailed articles about these or other topics. We would like to hear what would help you get more value out of your Firewalla.

Comments
0 comments
Please sign in to leave a comment.